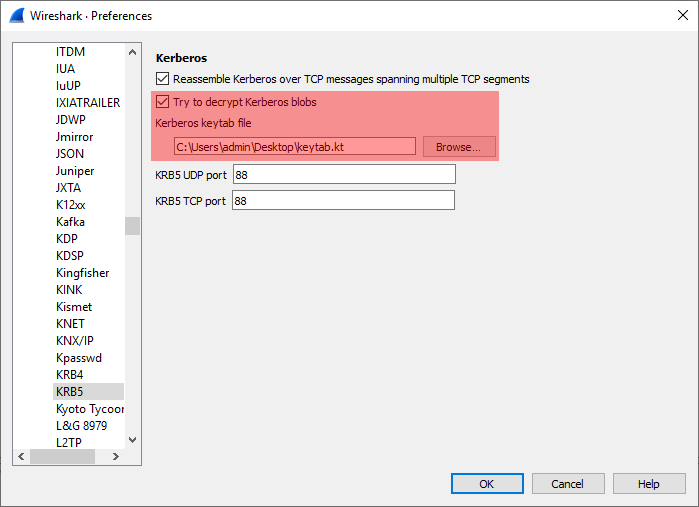
Have you ever wondered how to decrypt Kerberos/NTLM “encrypted stub data” fields 🔐 in Wireshark when analyzing Kerberos, RPC, LDAP… traffic?
➡️ Read how to do it on Tenable’s TechBlog: Decrypt Kerberos/NTLM “encrypted stub data” in Wireshark
This work led to two conference talks: